In the summer of 2016, Ledger, the market leader among hardware wallet manufacturers, introduced the Ledger Nano S. According to the company, this model sold over 1.3 million units. However, after three years, it was time for a new iteration. Following an extensive development period, Ledger launched the successor to the Nano S in May 2019.
In May 2019, the French manufacturer unveiled its new flagship, the Ledger Nano X. With the Nano X, Ledger promises the ‘next generation of hardware wallets’ and a ‘game changer for crypto investors worldwide.’
We’ve tested the Ledger Nano X to determine if it’s truly worth purchasing, even if you already own a Nano S. Additionally, we’ll demonstrate how the new hardware wallet from Ledger operates and how to set it up.
>> Buy your Ledger Nano X directly on the official Website from Ledger <<Comparison of the Ledger Nano S and the Ledger Nano X
❶ Bluetooth connection: The new Ledger Nano X offers you the possibility to manage cryptocurrencies on all popular smartphones via a Bluetooth connection, in conjunction with the Ledger Live App. The technical basis for this is an integrated Bluetooth chip that enables wireless connection. The Bluetooth connection is safety-certified, ensuring that your Private Keys will not be transferred.
❷ Significantly more memory: Compared to the Ledger Nano S, the internal memory has been significantly increased. With the Ledger Nano X, you can now manage up to 100 different cryptocurrencies simultaneously. This eliminates the hassle of uninstalling and installing apps, a limitation of the Ledger Nano S, which could only manage 5 apps at a time. The Ledger Nano X supports over 1,100 cryptocurrencies, surpassing other hardware wallets such as Trezor or the Digital Box.
❸ Larger screen: Ledger has not only increased the memory of the Nano X but also enlarged the screen. This enhancement allows addresses to be displayed in their entirety, eliminating the need for scrolling, as was necessary with the Ledger Nano S.
❹ Improved security chip: The central component of the hardware wallet has been revised and certified by the French cybersecurity authority ANSSI (Agence nationale de la sécurité des systèmes d’information).
Ledger Nano X: Price Comparison and Online Purchase Options
The price of the Ledger Nano X is currently 99 Euros (as of February 2024). Compared to other wallets, its price falls in the midrange. There are certainly more expensive hardware wallets available, as well as cheaper options.
However, the cheaper models, such as the Opendime (35 EUR for 3 pieces), the Trezor One (69 EUR), and also the predecessor model, the Ledger Nano S (59 EUR), offer a much smaller range of functions. The Ledger Nano X is therefore our clear winner in our Hardware Wallet Test 2019 in terms of price-performance ratio. Even more expensive hardware wallets such as the Trezor Model T or the Ellipal offer a smaller range of functions and can manage fewer cryptocurrencies.
In addition, Ledger’s security standard is industry-leading. No hardware wallet provider has been able to build such a brand and popularity in recent years. But Ledger is not only appreciated by private investors; numerous companies have also entered into partnerships with Ledger. The company cooperates with Neufund, blockchain.com, and Switcheo, among others. Samsung also announced a 2.6 million investment in the French company in April 2019.
If you are already convinced of the Ledger Nano X, you can buy it on Amazon, eBay, or directly from the manufacturer. However, we recommend that you buy from the manufacturer, as you will get the best price there and the product will be shipped directly from the manufacturer.
The price on Amazon and eBay may also be higher. Especially eBay also holds the danger of dubious traders. With the manufacturer, however, you have the security to get an original and not yet used Ledger. All prices on Ledger’s website are displayed directly in euros and include VAT.
>> Buy your Ledger Nano X directly on the official Website from Ledger <<
We ordered the Ledger Nano X directly from the official Ledger homepage. Despite the company being located in France, the shipping only took 3 working days. Payment methods include Bitcoin, Credit Card, Giropay, SOFORT, or Paypal, and shipping is free worldwide.
Ledger Nano X Review: Scope of Delivery
Upon receiving and unpacking the package, it’s crucial to first check that the packaging is unopened and the seal is undamaged. This step is very important because if the packaging has been tampered with, someone may have manipulated the ledger to steal your Bitcoin, Ether, or other cryptocurrencies later.
If anything on the packaging is broken or appears unusual, it’s better to replace the product immediately. It’s better to do so now than later when you may suffer a significant loss.
The following items are included in the scope of delivery:
- The Ledger Nano X Hardware Wallet
- A USB connecting cable
- A lanyard (although we recommend against carrying the wallet on it)
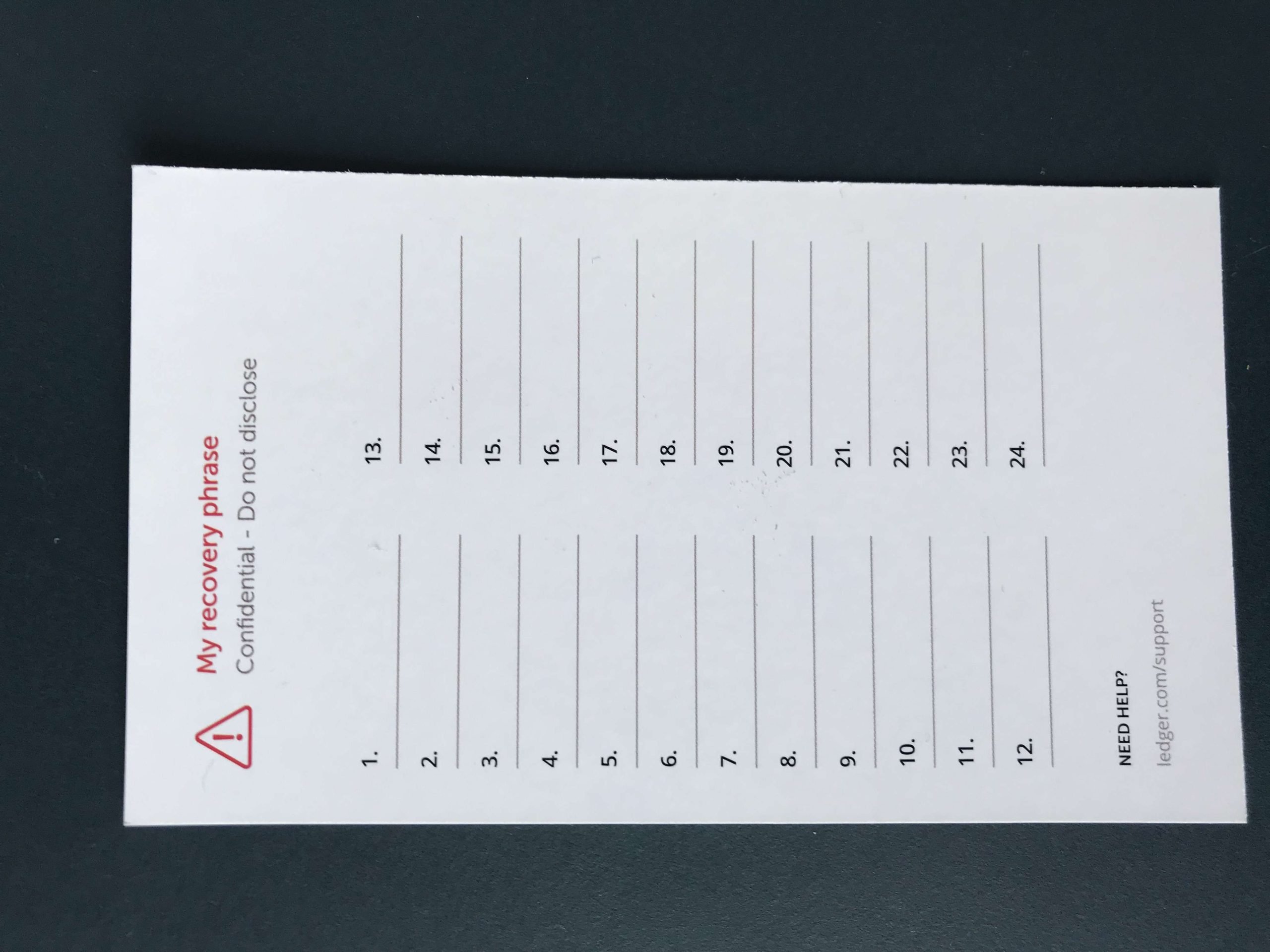
- Numerous cards and instructions on how to install the Nano X. This includes three cards where you can enter your recovery seed consisting of 24 words.
- Ledger Stickers
Ledger Nano X: First Steps
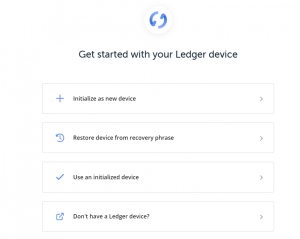
Install Ledger Live
- Set up a new device.
- Recover your account with the help of your Recovery Seeds if you already own a Ledger Nano X.
- Use a device that has already been set up by you.
- Buy another hardware wallet, which will redirect you to the ledger.com website.
Since you’ve likely just purchased your Ledger and are setting it up for the first time, click on “Set up new device“. In the next step, you’ll be asked which model you want to configure. Click on “Ledger Nano X”. Now your hardware wallet will be set up.
Managing Bitcoin, Ether, and Other Altcoins with the Ledger
Basic Operation
For each cryptocurrency such as Bitcoin, Ethereum, or XRP, you need to install an “App”. This is done via the “Manager” integrated in the Ledger Live software. To install apps, you must connect your Ledger to your computer and unlock it with your PIN. Only then can you proceed to install and uninstall new apps.
Under the menu item “Manager” you will find a large catalog of 1,100 apps. In addition to the crypto currency apps, there are also other apps that use the technology and security of the device. This includes an SSH agent or an app that can check the recovery seed.
The installation of the apps is super easy! Just click on “Install” and a few seconds later the app will be installed on your Ledger Nano X.
Recommendation: 2-factor authentication for the Ledger Nano X
We recommend to install the App Fido U2F Standard. This activates the 2-factor authentication, which is already standard on almost all cryptocurrency exchanges today. First you scan the barcode with your Google Authentiticator App, or a comparable app, with your mobile phone. You will then find a code in your app that updates every 30 seconds.
If you want to access your ledger in the future, you will be asked for this code. This is not a must for using the Ledger Nano X, as the hardware wallet already has the PIN security measure.
By using the 2-factor authentication app you increase the security of your hardware wallet even more! Especially since the Ledger Nano X can now manage 100 apps at the same time, you should take the time to install it. Unlike the Nano S, the limited disk space (on 5 apps) is no longer an excuse not to install the app.
Using Apps on the Ledger
Once you have installed the app on your Ledger, you can create an account in Ledger Live. Click on “Accounts” and then “Add account”:
If you want to create a wallet address for Bitcoin, you have to select “Bitcoin” now. Then follow the steps the ledgers ask you to follow. Among other things, you must confirm the account with the Ledger Nano X by pressing the two upper buttons. If you have also done this successfully, you can now start depositing Bitcoin, Ether, XRP or any other cryptocurrency.
You can also use your Ledger on any PC where Ledger Live is installed. Of course you have to go through all relevant security steps (enter PIN, password, 2-factor authentication etc.) each time you log in.
>> Buy your Ledger Nano X online <<
Receiving cryptocurrencies with the Nano X Ledger
If you want to deposit Bitcoin on your Ledger, you have to click on the tab “Receive”. Then you must select the correct account, in this case Bitcoin.
The next step is to connect your Ledger Nano X to your PC and select the Bitcoin app on your Ledger (double-click with both buttons).
If you have done this successfully, you can click on the blue button “Continue”.
Then you have to compare the address displayed on your Ledger Nano X with the address on your Ledger. Only if these two addresses match completely, you should confirm the address by pressing the two buttons on your Ledger Nano X.
You can now either copy the address (clipboard), use the scan function of the QR code or send it by mail.
Sending Cryptocurrencies with the Ledger Nano X
If you want to send Litecoin, Monero or other Altcoins to another wallet, it is also very easy. Just click on the menu item “Send” in the left navigation of Ledger Live.
Then select the respective account (e.g. “Bitcoin 1” in the screenshot) from which you want to send the cryptocurrency. On the following page you can set the receiving address, the amount and the network fee:
You can set the fees yourself. The higher the fees, the faster the transaction is normally processed. If you are not in a hurry, we recommend that you leave “Default” set. If you now click on “Continue”, your transaction will be sent. The display of the Ledger Nano X will now show you all the details of the transaction:
- The recipient address
- The fees charged for this transaction are as follows
If this information is correct, you can confirm the transaction on your Nano X.
The new Bluetooth function of the Ledger Nano X
When Ledger announced the new Bluetooth feature, there was a huge outcry in the crypto community that the feature is not secure and can be hacked. The fear was that hackers could hack the Bluetooth connection while sending and intercept the coins and redirect them to another address.
But this fear is wrong! Ledger explained that only non-critical data (not the private key and not the recovery seed) is transferred via Bluetooth. In addition, a physical keystroke on the Nano X ledger is always required to confirm transactions. Even if the Bluetooth connection is hacked, the transaction cannot be redirected to another address.
From a technical point of view, the French hardware wallet manufacturer also uses AES-based encryption, a state-of-the-art Bluetooth protocol that ensures authentication through the use of pairing. Your smartphone and the Nano X are “paired” by comparing two longer numbers on both devices. This process is shown in the following official Ledger video:
Advantages and disadvantages of the Ledger Nano X
The advantages of the Ledger Nano X:
✅ Best price/performance ratio in our hardware wallet comparison test
✅ Manage up to 100 crypto currencies on one hardware wallet simultaneously
✅ Over 1,100 supported crypto currencies
✅ Regular updates of Ledger
✅ Private keys are never connected to the PC or Internet, lie safely on the Ledger Nano X
✅ Manual confirmation of each transaction
✅ Ledger Live use via smartphone via Bluetooth connection
✅ Possibility to enable 2-factor authentication
Conclusion on the Ledger Nano X
After the Ledger Nano S has been sold more than 1.3 million times worldwide, Ledger has presented a worthy and innovative successor with the new Nano X. The device offers many new features and improvements (more memory, larger display, Bluetooth, …) which, in our opinion, justify the purchase of the Ledger Nano X, despite the ownership of a Ledger Nano S.
Especially if you want to manage larger amounts in cryptocurrencies, a hardware wallet is a mandatory investment. The price of 119 Euros is to be considered in relation to your assets: What are 119 EUR, if you want to secure your Bitcoin and Ether which are worth a thousand Dollars or more? In our opinion the investment in a hardware wallet is therefore an obligation and should be a matter of course.
The Ledger Nano X is our test winner in the big hardware wallet test and comparison and therefore our purchase recommendation for you.
Currently Ledger offers a discount campaign where you can buy a Ledger Nano S and a Ledger Nano X with 50% discount each. The total price is then 149,00€. If you want to buy the combo-package, just click on the following link:
>> Buy your Ledger Nano X directly on the official Website from Ledger <<
If you are not 100% sure which hardware wallet you want to buy, you can also check out our other hardware wallet reviews:
- Ledger Nano S Test
- Trezor One Test
- Trezor Model T Test
- ELLIPAL Test
- Bitbox 01 Test
- Opendime Bitcoin Stick Test
- BlochsTech
Subscribe to our daily newsletter!
No spam, no lies, only insights. You can unsubscribe at any time.